In today's rapidly evolving digital landscape, secure tunneling has emerged as a cornerstone of IoT device management within AWS. As organizations increasingly rely on the Internet of Things (IoT) to connect and manage devices remotely, ensuring the security of these devices has become paramount. This guide explores the significance of secure tunneling, its implementation strategies, and best practices to safeguard your IoT infrastructure effectively.
As the number of connected devices continues to grow exponentially, the demand for secure communication channels in IoT environments has surged. AWS IoT Device Management provides robust tools and features to facilitate secure tunneling, enabling businesses to remotely access and control devices without exposing them to public networks. This article delves into the nuances of secure tunneling, its importance, and how AWS IoT Device Management can be leveraged effectively.
Whether you're a developer, IT professional, or decision-maker, understanding secure tunneling for AWS IoT device management is essential for safeguarding your organization's assets. This guide will walk you through the concept, implementation strategies, and best practices to ensure your IoT infrastructure remains secure and efficient.
Read also:Jimmy Fallon Birthday Celebrating The Life And Career Of A Latenight Legend
Table of Contents
- Understanding Secure Tunneling for AWS IoT Device Management
- What is AWS IoT Device Management?
- The Importance of Secure Tunneling in IoT
- How Secure Tunneling Functions with AWS IoT
- Advantages of Secure Tunneling for AWS IoT
- Implementation Strategies
- Best Practices for Secure Tunneling
- Common Challenges and Solutions
- Real-World Applications of Secure Tunneling
- Emerging Trends in Secure Tunneling for IoT
- Conclusion
Understanding Secure Tunneling for AWS IoT Device Management
Secure tunneling involves the creation of encrypted communication channels between devices and servers, ensuring that data remains protected during transmission. Within the context of AWS IoT Device Management, secure tunneling empowers organizations to access and manage IoT devices remotely without exposing them to public networks. This approach not only minimizes the risk of unauthorized access but also safeguards against potential cyberattacks.
AWS IoT Device Management simplifies the process of organizing, monitoring, and managing IoT devices at scale. By integrating secure tunneling capabilities, businesses can enhance their IoT infrastructure's security and reliability. This section explores the fundamental concepts and importance of secure tunneling in modern IoT ecosystems, offering a deeper understanding of its role in protecting critical assets.
What is AWS IoT Device Management?
AWS IoT Device Management is a comprehensive platform designed to help organizations manage their IoT devices efficiently. It offers features such as device provisioning, monitoring, and software updates, all within a secure and scalable environment. With AWS IoT Device Management, businesses can effortlessly track device health, apply patches, and enforce security policies across their IoT fleet.
Some of the standout features of AWS IoT Device Management include:
- Device grouping and tagging for streamlined organization
- Remote device troubleshooting capabilities
- Secure firmware updates to maintain device integrity
- Compliance monitoring to adhere to industry standards and regulations
By leveraging AWS IoT Device Management, organizations can optimize their IoT operations while ensuring the highest level of security, enabling them to focus on innovation and growth.
The Importance of Secure Tunneling in IoT
In an increasingly interconnected world, securing IoT devices is crucial for protecting sensitive data and maintaining operational integrity. Secure tunneling plays a pivotal role in achieving this goal by establishing encrypted communication channels between devices and servers. This ensures that even if a connection is intercepted, the data remains unreadable to unauthorized parties.
Read also:Discover Everything You Need At Walmart Supercenter Auburn Al
The significance of secure tunneling in IoT extends beyond basic data protection. Key reasons why secure tunneling matters include:
- Guarding against data breaches that could compromise sensitive information
- Preventing unauthorized access to devices and networks
- Enhancing privacy and ensuring compliance with regulatory standards
Without secure tunneling, IoT devices could be vulnerable to various cyber threats, including malware, ransomware, and phishing attacks. By implementing secure tunneling solutions, organizations can significantly mitigate these risks and safeguard their assets, fostering trust and confidence in their IoT ecosystems.
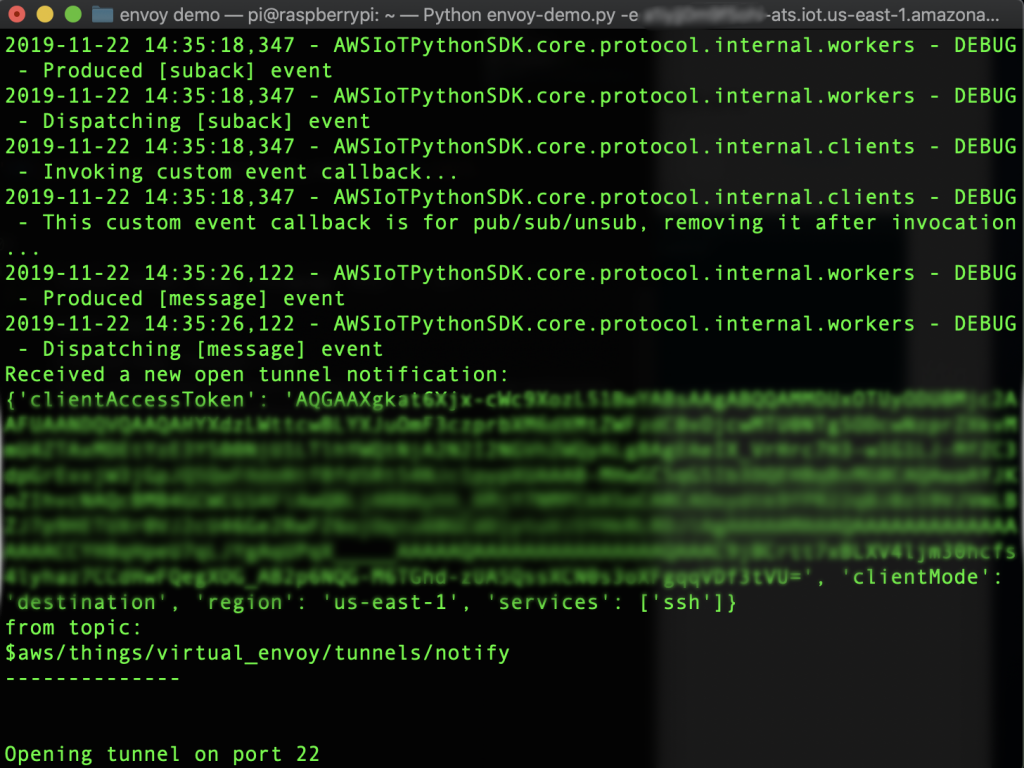
How Secure Tunneling Functions with AWS IoT
Secure tunneling in AWS IoT Device Management utilizes advanced encryption protocols to establish secure connections between devices and servers. The process begins with the creation of a secure channel using Transport Layer Security (TLS), which ensures data integrity and confidentiality during transmission. Once the channel is established, devices can communicate with servers without exposing sensitive information to public networks.
The key components of secure tunneling in AWS IoT include:
- TLS encryption for robust data protection
- Device authentication to verify the identity of connected devices
- Access control policies to govern who can access specific resources
By integrating these components, AWS IoT Device Management provides a robust framework for secure communication in IoT environments, enabling organizations to operate with confidence and efficiency.
Advantages of Secure Tunneling for AWS IoT
Implementing secure tunneling for AWS IoT device management offers numerous benefits that enhance both security and operational efficiency. These advantages include:
- Enhanced Security: Protects devices and data from unauthorized access and cyber threats, ensuring the integrity of IoT operations.
- Improved Efficiency: Simplifies remote device management and troubleshooting, reducing the time and resources required to maintain IoT infrastructure.
- Scalability: Supports large-scale IoT deployments without compromising performance, allowing organizations to grow their IoT ecosystems seamlessly.
- Compliance: Ensures adherence to industry standards and regulations, minimizing legal and reputational risks associated with non-compliance.
These benefits make secure tunneling an indispensable component of any IoT infrastructure, empowering businesses to thrive in an increasingly connected world.
Implementation Strategies
Successfully implementing secure tunneling for AWS IoT device management requires a strategic approach that encompasses planning, execution, and ongoing maintenance. Below are the key steps involved in the process:
Step 1: Set Up AWS IoT Core
AWS IoT Core serves as the foundation for managing IoT devices and establishing secure connections. To set it up effectively:
- Create an AWS account and navigate to the IoT Core console to access the platform's capabilities.
- Register your devices and assign unique identifiers to ensure proper tracking and management.
- Configure security policies and access controls to define permissions and restrict unauthorized access.
Step 2: Configure Device Security
Securing IoT devices is essential to prevent unauthorized access and potential cyberattacks. Key steps in this process include:
- Implementing strong authentication mechanisms, such as certificates and tokens, to verify device identities.
- Using encryption protocols, such as AES and RSA, to secure data transmission and protect sensitive information.
- Regularly updating firmware and software to address vulnerabilities and ensure devices remain secure.
Step 3: Establish Secure Connections
Once the infrastructure is in place, establishing secure connections using AWS IoT Device Management's tunneling capabilities is crucial. This involves:
- Creating a secure channel using TLS encryption to safeguard data during transmission.
- Testing the connection to ensure data integrity and confidentiality, identifying and resolving any issues promptly.
- Monitoring and maintaining the connection for optimal performance, addressing any disruptions or anomalies as they arise.
Best Practices for Secure Tunneling
To maximize the effectiveness of secure tunneling for AWS IoT device management, organizations should adhere to the following best practices:
- Regularly audit security policies and access controls to identify and address potential vulnerabilities.
- Implement multi-factor authentication to add an extra layer of security, making it more difficult for unauthorized users to gain access.
- Monitor device activity for signs of unauthorized access, enabling swift detection and response to potential threats.
- Keep firmware and software up to date with the latest patches to address known vulnerabilities and enhance security.
By following these best practices, organizations can ensure their IoT infrastructure remains secure and reliable, protecting their assets and maintaining operational integrity.
Common Challenges and Solutions
While secure tunneling offers numerous benefits, it also presents challenges that must be addressed to achieve successful implementation. Common challenges include:
- Complexity: Managing large-scale IoT deployments can be complex. Solution: Utilize automated tools and scripts to streamline processes and reduce the burden on IT teams.
- Cost: Implementing secure tunneling solutions can be expensive. Solution: Optimize resource usage and explore cost-effective alternatives, such as leveraging open-source tools and services.
- Compatibility: Ensuring compatibility across different devices and platforms can be challenging. Solution: Standardize protocols and interfaces to facilitate seamless integration and communication.
By proactively addressing these challenges, organizations can overcome obstacles and achieve successful secure tunneling implementations, enhancing their IoT infrastructure's security and efficiency.
Real-World Applications of Secure Tunneling
Several organizations have successfully implemented secure tunneling for AWS IoT device management, demonstrating its versatility and effectiveness across various industries. For instance:
- Manufacturing Industry: A leading manufacturer leverages secure tunneling to monitor and control industrial equipment remotely, reducing downtime and improving operational efficiency.
- Healthcare Sector: A healthcare provider employs secure tunneling to manage medical devices, ensuring patient data remains protected and compliant with stringent regulations.
These examples illustrate how secure tunneling can be tailored to meet the unique needs of different industries, enhancing security and driving innovation.
Emerging Trends in Secure Tunneling for IoT
The future of secure tunneling for IoT is promising, with emerging technologies and trends reshaping the landscape. Key trends to watch include:
- Artificial Intelligence: AI-powered security solutions will enhance threat detection and response capabilities, enabling organizations to proactively address potential risks.
- Quantum Encryption: Quantum-based encryption methods will provide unprecedented levels of security, protecting data against future threats and advancements in computing power.
- Edge Computing: Edge computing will enable faster and more efficient data processing at the device level, reducing latency and enhancing overall performance.
By staying informed about these trends, organizations can prepare for the future of secure tunneling in IoT, ensuring their infrastructure remains secure and competitive in an ever-evolving digital landscape.
Conclusion
Secure tunneling for AWS IoT device management is a critical component of modern IoT infrastructure, enabling organizations to protect their devices and data while ensuring operational efficiency. By leveraging AWS IoT Device Management's robust features and secure tunneling capabilities, businesses can safeguard their assets and thrive in an increasingly connected world.
We encourage you to take action by implementing secure tunneling solutions in your IoT environment. Share your thoughts and experiences in the comments below, and explore other articles on our site for more information on IoT security and management. Together, we can build a more secure and efficient IoT ecosystem for the future.