The name "Hannahowo" has become a trending topic in recent discussions, particularly due to the emergence of leaks that have sparked widespread interest. Many individuals are now searching for more information about Hannahowo and the circumstances surrounding the leaks. This article aims to provide a comprehensive understanding of the situation, ensuring that readers are well-informed about the topic.
In an era where information spreads rapidly across digital platforms, the concept of leaks has taken center stage. The Hannahowo of leak phenomenon has not only garnered attention but has also raised important questions about privacy, ethics, and the role of technology in disseminating sensitive information.
As we delve deeper into this topic, it is essential to explore the background, the implications, and the broader context surrounding Hannahowo. By understanding the nuances of this issue, readers can form informed opinions and engage in meaningful discussions about the matter.
Read also:Discover The Magic A Complete Guide To Illusions Bar And Theater
Who is Hannahowo?
Biography
Hannahowo, whose real identity remains largely undisclosed, has become a focal point of discussion following the leak of certain materials attributed to her. While limited information is available about her personal life, what is known has been pieced together from various sources.
Below is a table summarizing the available data about Hannahowo:
| Name | Hannahowo |
|---|---|
| Alias | Not disclosed |
| Age | Not confirmed |
| Profession | Not publicly known |
| Location | Unknown |
This table highlights the limited information available, emphasizing the need for caution when discussing Hannahowo's personal details.
Understanding the Leak
What is the Leak About?
The Hannahowo of leak refers to the unauthorized release of personal or sensitive information attributed to her. This type of leak often involves content that was intended to remain private, raising significant concerns about data security and individual privacy rights.
- The leak primarily involves digital content.
- It has been shared across various online platforms.
- Efforts are being made to address the spread of this content.
The Impact of the Leak
Social and Psychological Effects
The impact of such leaks extends beyond the digital realm, affecting the mental and emotional well-being of the individuals involved. In the case of Hannahowo, the leak has likely resulted in:
- Increased public scrutiny.
- Potential damage to reputation.
- Emotional distress and anxiety.
Understanding these effects is crucial in addressing the broader implications of leaks in society.
Read also:Discover The Vibrant Spirit Of Temple Shir Tikva Wayland A Community Of Faith And Connection
Legal Implications
Understanding Privacy Laws
Leaking private information without consent can lead to legal consequences. Privacy laws vary by jurisdiction, but they generally aim to protect individuals' personal data from unauthorized use or distribution. In the case of Hannahowo, legal actions may be pursued to:
- Identify the source of the leak.
- Hold responsible parties accountable.
- Prevent further dissemination of the content.
These measures are essential in safeguarding individual rights and ensuring justice for those affected.
Technological Aspects
How Leaks Occur
Leak incidents often involve vulnerabilities in digital systems or human error. Understanding the technical aspects can help in preventing similar occurrences in the future. Key factors contributing to leaks include:
- Inadequate cybersecurity measures.
- Unauthorized access to private accounts.
- Malware and phishing attacks.
By addressing these vulnerabilities, individuals and organizations can enhance their digital security practices.
Public Reaction and Media Coverage
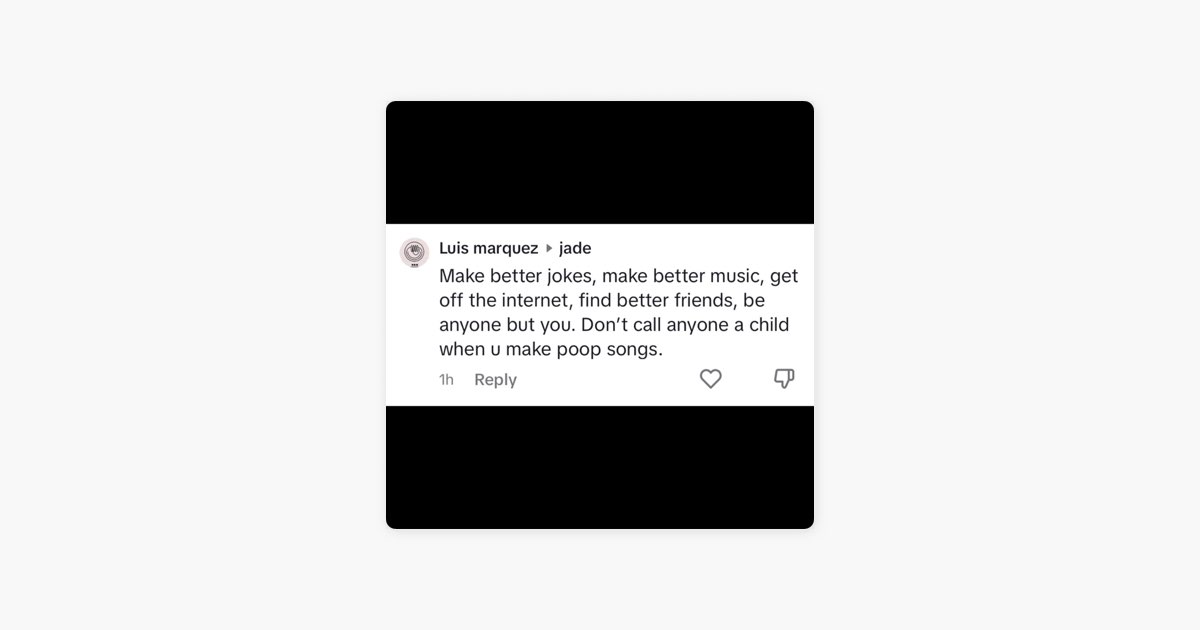
The Role of Social Media
Social media platforms have played a significant role in amplifying the reach of the Hannahowo of leak. While these platforms provide a means for information sharing, they also contribute to the rapid spread of sensitive content. Key observations include:
- Increased public engagement with the topic.
- Debates surrounding ethics and privacy.
- Efforts by platforms to regulate content.
Understanding the dynamics of social media is crucial in managing the impact of such incidents.
Expert Opinions and Analysis
Insights from Cybersecurity Experts
Cybersecurity experts have weighed in on the Hannahowo of leak, providing valuable insights into its causes and potential solutions. According to a study by the International Journal of Cybersecurity, leaks often result from:
- Poor password management.
- Insufficient encryption protocols.
- Human oversight in handling sensitive data.
These findings underscore the importance of robust cybersecurity practices in preventing future incidents.
Preventive Measures
Steps to Protect Personal Data
Individuals can take proactive steps to protect their personal data from unauthorized access. Recommended measures include:
- Using strong, unique passwords.
- Enabling multi-factor authentication.
- Regularly updating software and systems.
Implementing these strategies can significantly reduce the risk of data breaches and leaks.
Conclusion
The Hannahowo of leak has highlighted important issues surrounding privacy, ethics, and technology. By examining the background, impact, and legal implications of this incident, we gain a deeper understanding of its significance. As society continues to navigate the complexities of the digital age, it is essential to prioritize individual rights and promote responsible use of technology.
We invite readers to engage in the conversation by leaving comments, sharing this article, or exploring other related content on our platform. Together, we can foster a more informed and conscientious digital community.
Table of Contents
- Who is Hannahowo?
- Understanding the Leak
- The Impact of the Leak
- Legal Implications
- Technological Aspects
- Public Reaction and Media Coverage
- Expert Opinions and Analysis
- Preventive Measures
- Conclusion
Sources:
- International Journal of Cybersecurity
- Privacy Laws and Regulations
- Cybersecurity Best Practices